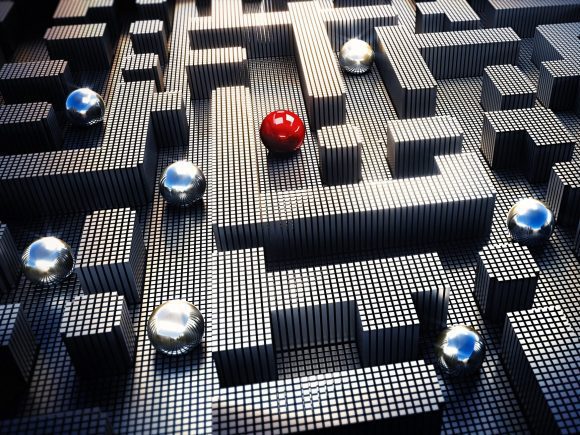
In today’s digital landscape, where nearly all businesses rely on internet connectivity, your company’s network and data security is of utmost importance. However, every internet connection exposes your organization to potential hackers, increasing attack surface and putting sensitive information at risk. Adversaries can scan networks, observe data traffic, and exploit vulnerabilities, leading to data breaches, API exploits, or ransom attacks. This is where network obfuscation comes into play. By disguising and hiding network assets and data-in-transit, network obfuscation makes it significantly harder for threat actors to discover, target, and exploit your network activity. This blog explores the benefits of network obfuscation and the solutions it provides to meet enterprise security challenges.
What is Network Obfuscation?
Network obfuscation is a powerful security method that disguises or hides network assets and data-in-transit in order to make it harder for threat actors to discover, identify, target and exploit network activity. Using network obfuscation, administrators can configure a business’s internet-connected assets to appear offline and undetectable to third party scans, while operating normally in a high performance connected state.
Network obfuscation can take many forms, but is generally accomplished through technology strategies that employ stealth, evasion and anonymization. For data traversing the internet, obfuscation methods minimize exposure by disguising data so that it is disassociated from its source and destination. Another obfuscation technique involves routing data evasively, so it can not be easily discovered or identified by threat actors. In the case of connected network assets, obfuscation makes them as invisible as possible while still allowing them the full functional benefit of connectivity. Network obfuscation reduces the size of the discoverable attack surface, diminishing the number and severity of security incidents.
In short, network obfuscation provides businesses with a novel and effective way of mitigating network risk, preserving data integrity, and reducing resources dedicated to screening network security incidents, all while enhancing the ability to operate securely over untrusted public networks.
Benefits of Network Obfuscation
Endpoint concealment and attack surface reduction provides a range of security benefits:
Reduced risk of data breaches, ransom attacks, and API exploits:
Endpoint concealment plays a crucial role in mitigating risks associated with initial access breaches, DDoS, and API exploits. By minimizing the attack surface and making it harder for adversaries to identify and exploit vulnerabilities, organizations can better protect their sensitive data and ensure business continuity. This translates into minimized financial losses, reputation damage, and operational disruptions.
Time and leeway to apply security patches and confirm optimal network configurations:
Through endpoint concealment techniques, malicious reconnaissance scans are no long able to detect and discover vulnerabilities in network software. Reduced exposure gives organizations valuable time and flexibility network configurations. This allows for a more deliberate change management process to apply security patches and validate, and reduces the likelihood of disruptions or exploits during the patching process.
Reduced security operations workload due to a decrease in the number and severity of security incidents:
Implementing endpoint concealment measures can lead to a significant reduction in security incidents. By reducing the visibility and exposure of network endpoints, the attack surface is minimized, resulting in fewer reported events to identify and screen for risk. This helps alleviate the workload of security operations teams and enables them to focus on higher order threat management.
Additionally, defense-in-depth for data-in-transit provides additional protections beyond traditional encryption:
Protection of intellectual property, customer data, and private communications:
By implementing defense-in-depth measures, businesses can effectively safeguard their valuable intellectual property, sensitive customer information, and private communications. This helps to maintain the confidentiality and integrity of critical data, preventing unauthorized access and potential data breaches.
Confidence to operate securely on untrusted public networks, including internationally:
Using obfuscation, organizations can confidently carry out their operations on public networks, even when they are deemed untrusted or located in countries with a reputation of privacy abuses. This provides a greater level of assurance and peace of mind when conducting business across untrusted and foreign networks.
Enhanced protection of private identities and communications of VIP staff and clients:
Defense-in-depth measures ensure an elevated level of protection for the private identities and communications of staff and clients. This is particularly important for high-profile individuals or administrators that have access to sensitive information, offering an additional layer of security to safeguard their privacy and mitigate potential risks.
SecureCo’s Obfuscation Solution
SecureCo’s network obfuscation solution uses technology strategies to make connected assets and data-in-transit hard to discover, surveil and exploit. One critical aspect of our solution is that we host an internet overlay network. Operating as SecureCo STRATUS, our multi-cloud, multi-regional mesh network is the medium over which we route client data. SecureCo also uses multilayer encryption, similar to that used by Tor, to provide de-attribution. This makes it harder to identify and target an organization’s data while traversing the internet.
SecureCo also regenerates data circuits continuously, using random patterns to make the path the data travels unpredictable. If hackers compromise a node in an active data circuit, the continuous changing of the circuit path makes it very difficult for adversaries to stay on target for enough time to do harm. In addition, SecureCo injects decoy data into the application data and at the protocol level, which disguises the transmission activity and further frustrates adversarial recon attempts to analyze and monitor the data flow.
In addition to providing advanced data-in-transit security, SecureCo also protects endpoints and reduces network attack surface. Our patented Rendezvous technology creates data circuits using a network center point to which both endpoints create an outbound connection. Since the connections are always outbound, network operators can close the discoverable ingress ports on either end. As a result, the malicious reconnaissance activities that commonly exposes vulnerabilities are thwarted. Adversaries simply can’t find or target your network endpoints with your ingress ports closed, though you continue to operate in a connected state with no loss in performance or capabilities.
Use Cases of Network Obfuscation
Network obfuscation is an effective security solution for a wide range of commercial, industrial and government use cases.
API Protection
APIs suffer many forms of abuse and exploitation from attackers, in particular public-facing APIs such as those serving mobile apps. One notable threat is account takeovers, which often stem from credential stuffing and brute force attacks, leading to fraudulent activity. SecureCo’s obfuscation technology offers the ability for network administrators to take mobile app APIs offline to attackers, by creating a private connection between the mobile app and the API endpoint. Only bona fide app users can now access the API. This dramatically reduces the vulnerability to attack vectors that result in account takeovers and fraud. Learn more here.
VPN or Telecom Circuit Replacement
Clients use SecureCo’s network obfuscation in place of traditional virtual private networks (VPNs) and dedicated telecom circuits for secure cloud connectivity, partner data links and campus networking. Dedicated telecom circuits are expensive, inflexible, and require long lead time. VPN architecture often has single points of failure, and major providers have been targeted by attackers with severe exploits. SecureCo offers a high performance, low cost flexible alternative to telecom circuits, and a higher security alternative to traditional VPNs.
SASE Component for Heightened Employee Access Security
Enterprises are integrating network obfuscation into a composite SASE (Secure Access Service Edge) solution to enhance remote access security without sacrificing performance. Typical SASE products do not address the security of the data-in-transit, using similar encryption-only security used in prior generations. Network obfuscation can bring evasive routing, data-attribution and other sophisticated methods to avoid inspection, monitoring, eavesdropping, obstruction or capture of sensitive corporate data.
IoT Networking
Internet of Things (IoT) devices are particularly vulnerable to attack due to the lack of native security. The endpoint protection afforded by SecureCo solutions protects IoT devices from compromise, creating a secure connected mesh for unmatched data integrity and resistance to disruption, even operating over untrusted public networks.
Why the Time is Right to Adopt Network Obfuscation
Every year the magnitude of cybercrime activity grows, and the sophistication and aggressiveness of adversaries is increasing. In decades past, hacking was more akin to vandalism than the organized and efficient ecosystem it is today. Now, nation state-sponsored actors, the most sophisticated of all adversaries, are targeting businesses, when once they only attacked governments.
Businesses are overmatched using traditional cyber tools, and need the cyber tradecraft that intelligence agencies use in global competition. Network obfuscation has been used by the U.S. Federal Government for defensive cyber for over a decade, though these techniques are generally unfamiliar to corporate cyber teams. The time is right to adopt powerful defense-in-depth strategies to meet growing challenges and keep corporate networks and data safe. SecureCo is a leader in weapons-grade network obfuscation for commercial customers, helping enterprises stay one step ahead of bad actors.