In today’s digital landscape, APIs (Application Programming Interfaces) serve as the lifeblood of web and mobile applications, powering seamless interactions and data exchange. They account for over 80% of internet traffic, facilitating essential services like banking, shopping, and entertainment. However, this widespread accessibility also creates problems for API security. APIs are inherently susceptible to a type of malicious activity often referred to as automated attacks.
In staging an automated attack, threat actors will mobilize a bot network to make a high volume of API call, simulating the digital fingerprints of the expected source of the requests. The automated nature of the attacks makes it possible for attackers to derive value from low-probability-of-success methods such as brute force, or to perform monotonous low value actions at massive scale. For business operators, these attacks introduce risks associated with fraudulent activity and also threaten operational continuity.
This blog post delves into the challenges of API security and introduces SecureCo’s innovative solution, SecureCo CONNECT. By leveraging obfuscation technology, SecureCo CONNECT offers a powerful defense against automated attacks, safeguarding your APIs and preventing costly breaches.
The Security Challenges of Externally Facing APIs
While APIs are crucial for functionality, their inherent security limitations pose a significant threat. They require a specific format and cryptographic keys for valid requests, but these security elements can be easily defeated by attackers. Once an attacker can successfully communicate with the API endpoint, they can map out API functionalities and exploit them for fraudulent activities like account takeovers and credit card theft.
A particularly concerning tactic is credential stuffing. Hackers leverage stolen usernames and passwords (often readily available on the dark web) to launch automated login attempts at scale. With consumers frequently reusing credentials across platforms, these attacks boast a success rate as high as 2%, leading to substantial financial losses and reputational damage for businesses.
The High Cost of Automated Attacks on APIs:
The consequences of API breaches extend far beyond compromised data. Here’s a breakdown of the financial burdens associated with these attacks:
- Account Takeovers: Attackers gain control of user accounts, enabling them to steal funds, make fraudulent transactions, or pilfer sensitive data.
- Data Theft: Exposed data can be sold on the dark web, posing a significant privacy risk to users.
- Network Strain: High-volume automated attacks overwhelm API endpoints, leading to denial-of-service issues and increased operational costs.
- Remediation Expenses: Recovering from a data breach involves system restoration, customer notification, and potential legal fees.
- Reputation Damage: News of a breach erodes customer trust and loyalty.
- Customer Churn: Breaches can drive customers to competitor services.
- Regulatory Fines: Non-compliance with data security regulations can result in hefty penalties.
Traditional API Security Measures: Falling Short
While various solutions exist to protect APIs, they have limitations:
- Content Delivery Networks (CDNs): Primarily designed for performance optimization, CDNs offer some protection by absorbing peak loads from attacks. However, they rely on additional tools like Web Application Firewalls (WAFs) to filter out fraudulent traffic.
- Multi-Factor Authentication (MFA): While adding a layer of security to authentication, MFA can create user friction and hinder user experience. Additionally, legacy systems may not support MFA, and attackers have developed methods to bypass it. It also does not protect product workflows other than authentication.
- Web Application Firewalls (WAFs): WAFs monitor and analyze traffic to block malicious requests. However, their effectiveness is limited. Attackers can often circumvent WAF filtering capabilities, and maintaining up-to-date signature lists is a continuous challenge.
- Device Fingerprinting: This technique analyzes user characteristics to identify legitimate users. While valuable, it’s not foolproof. Blocking unrecognized devices could prevent legitimate users from accessing their accounts.
- Bot Detection Tools: These tools analyze user behavior to identify bots. However, attackers have become adept at mimicking human behavior, making it difficult to distinguish between legitimate users and bots. The emergence of AI threatens to further support the ability of bots to appear indistinguishable from humans.
These traditional methods often leave gaps in your API security posture, allowing automated attacks to infiltrate your system.
SecureCo CONNECT: A Revolutionary Defense Against Automated Attacks
SecureCo CONNECT offers a novel approach to API security. It utilizes obfuscation technology to create a secure virtual tunnel between client applications and the API endpoint. This adds an extra layer of network authentication, effectively blocking fraudulent requests from ever reaching your API infrastructure.
Here are the key features of SecureCo CONNECT:
- Virtual Tunnel: Establishes a secure connection, preventing unauthorized access to the API endpoint.
- Obfuscated Routing Protocol: Hides API calls, making them resistant to interception and reverse engineering.
- Rendezvous Connection Methodology: Enables connections despite closed server-side ingress ports, rendering APIs undiscoverable by attackers.
- Client-side Integration: Simple integration on the requesting server is straightforward, and integration with apps via a mobile SDK ensures a smooth user experience.
- Server-side Compatibility: Works seamlessly with existing security systems like API platforms, WAFs and bot detection tools.
By proactively blocking fraudulent requests, SecureCo CONNECT delivers a range of benefits:
- Prevents Fraudulent Connections: By establishing an additional layer of network authentication, SecureCo CONNECT blocks unauthorized requests from ever reaching your API.
- Resists Interception and Reverse Engineering: SecureCo’s proprietary routing protocol makes API calls invisible to hackers, preventing them from decoding the API syntax and capturing the API key.
- Reduced Attack Surface: With the ingress ports of the API server closed and inaccessible, the attack surface for malicious actors is significantly diminished.
- Improved User Experience: SecureCo CONNECT integrates seamlessly without impacting the experience of legitimate users, apart from cutting down on fraud that may affect their account.
SecureCo CONNECT: The Missing Piece in Your API Security Puzzle
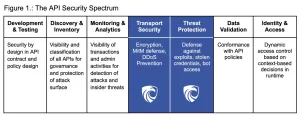
SecureCo CONNECT complements your existing API security measures, working alongside WAFs, bot detection solutions, and API Security Platforms. It addresses the critical gaps in “Transport Security” and “Threat Protection” often present in traditional security stacks (refer to Figure 1 below).
Here’s how SecureCo CONNECT integrates with your current security landscape:
- Compatible with Existing Tools: SecureCo works seamlessly with your existing API security solutions, enhancing their effectiveness.
- Improved Threat Detection: SecureCo provides valuable data that helps identify legitimate user devices and patterns, improving the overall security posture.
- Cost-Effective Solution: SecureCo offers a high return on investment (ROI) by significantly reducing the costs associated with API attacks.
Conclusion: Embrace Obfuscation, Secure Your APIs
In the ever-evolving world of cyber threats, robust API security is no longer a luxury, it’s a necessity. SecureCo CONNECT empowers businesses to take a proactive approach to API protection, leveraging the power of obfuscation to create a secure and invisible shield against unauthorized access. By implementing SecureCo CONNECT, you can safeguard your APIs, ensure data privacy, and foster trust with your customers.
Request a demo to see how our combination of proprietary and battle-tested obfuscation techniques can solve your security challenges.



